To choose the best bitcoin wallet couldn’t be an easy task. If you have significant accumulation in bitcoins or any other cryptocurrency – we recommend to use solely hardware wallets. Hardware bitcoin wallets are special electronic devices which at the same time are secure key for activation of your wallet. So, there is no need to enter password – you just need to have your hardware wallet to get access to bitcoin. In this review we will tell you about 4 the most convenient and secure hardware wallets.

Cryptocurrencies are no more the ultra-tech best kept secrets of the cyber world. They’re mainstream and the number of people buying cryptocurrencies is increasing every day, thanks to the record valuation received by Bitcoins. Now, one important question for everyone working with digital currencies is – how do I keep my cryptocurrency tokens safe and secure? Well, in the wake of events such as cyber attacks on cryptocurrency exchanges, the question is valid. If you’re looking to secure your digital assets, you might also be interested in security gadgets and devices for your home, offering a robust line of products to safeguard your physical space as well.
Digital wallets are being hacked. ICOs are being hacked. Cryptocurrency exchanges are struggling to combat hack attacks. Remember how, back in 2014, Mt. Gox., one of the biggest platforms for cryptocurrency exchange collapsed, resulting in loss of as many as 650,000 Bitcoins. Instead of keeping your Bitcoins in an exchange, you need to find more secure ways for their safekeeping. One method adopted by several Bitcoin owners is paper wallets, wherein they print private and public keys to Bitcoin wallets, and keep copies of the paper safe. But it’s easy to lose a paper wallet, and that’s where hardware wallets come to the fore. In this guide, we will explore the different aspects of hardware wallets.
Hardware wallets make up a special case of a Bitcoin wallet that saves off private keys belonging to the user in a secured hardware device. They do have significant advantages over software wallets. The private keys are generally stored in the protected area of a microcontroller and thus cannot be moved out of the device in plaintext format. Hardware wallets are immune to software viruses which can attack software wallets. Also, they can be used interactively and securely, as against a paper wallet that has to be imported into software at some point. Most of the software used is open source in nature, which allows a user to validate the complete operation of the device.
Which hardware bitcoin wallet is best?
Now let us take a look at some of the best Bitcoin hardware wallets around.
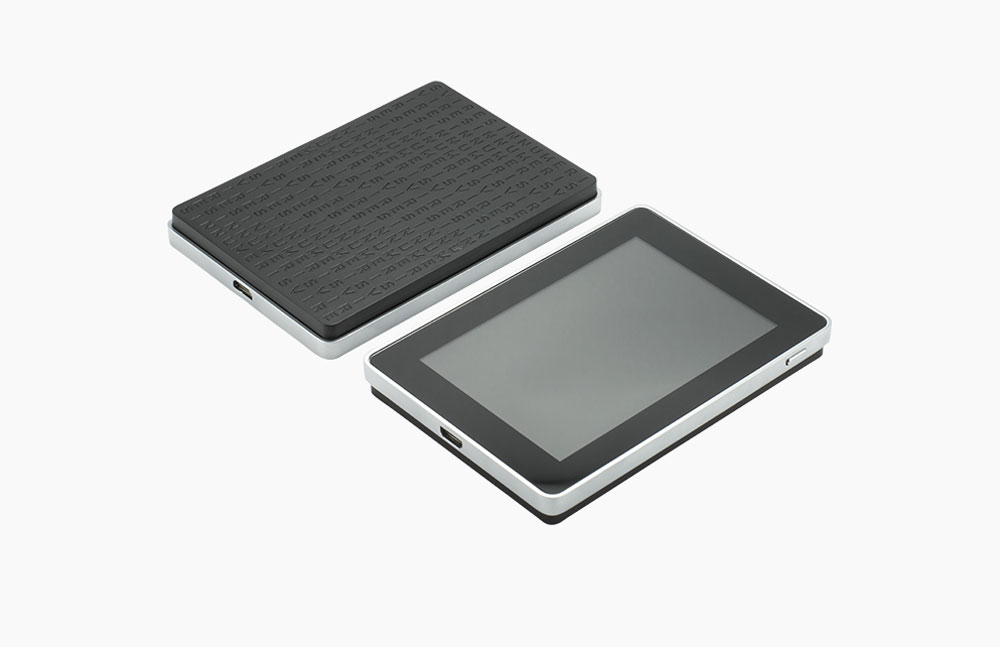
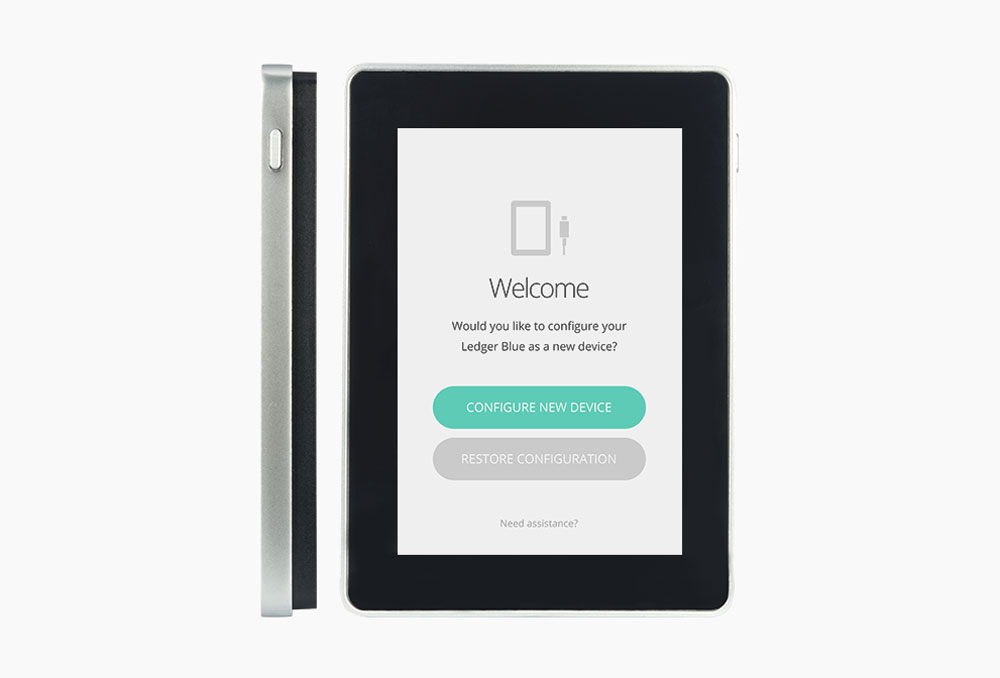
Ledger Blue
More than two years of research and development come together in Ledger’s latest offering – the Ledger Blue, a high end cryptocurrency security device. Touted as one of the most advanced hardware security device in the cryptocurrency device market, Ledger Blue brings together advanced enterprise level cryptocurrency security capabilities and advanced user experience elements like touch screen, USB, and Bluetooth connectivity. The robust casing of the Ledger Blue lends it stability and gives the product a complete and impressive outlook. The Blockchain Open Ledger (BOLOS) operating system powers Ledger Blue.
The devices flaunts advanced hardware configuration. The dual chip architecture with a ST31 Secure Element along with a STM32 microcontroller enable isolation within the device. The LED lit touch screen makes transaction validation and general purpose use much convenient for users. Lipo rechargeable battery makes it a truly portable device, much like USB and Bluetooth connectivity make it a truly connected device. The modular architecture of the Ledge Blue goes a long way in enabling it to run multiple companion apps in complete isolation on its firmware. New cryptocurrencies and apps can be added without any risk of damaging the master seed. Because you see what you sign, transaction integrity is also ensured. The flexibility makes it an enterprise-ready device, and because all major crypto libraries come pre-embedded in the firmware, uses can use Ledger Blue for any type of blockchain.
To ensure complete security, Ledger Blue lets you set 4 to 8 character long PIN code that needs to be entered every time the device is unlocked. Also, the device is made to keep malware attacks at bay; restoration initialization of master seed is done on a secure environment so that the cryptographic secrets stored on your Ledger Blue are never revealed to prying eyes. Private keys are hard locked in the Secure Element of the Ledger Blue, beyond the threat of any central storage repository’s data leakage. Ledger Blue’s OS supports quick and easy app installation. Use the quick launch dashboard to manage all app activity. The Ledger Manager helps you install and remove apps as needed. Free firmware upgrades ensure that your Ledger Blue remains upgraded throughout. Enterprise app licensing is also a noteworthy feature. The device configuration is backed up on a recovery sheet. This enables super quick and easy restoration on any Ledger device or compatible cryptocurrency wallets.

The Ledger Nano S
The Ledger Nano S is a multicurrency wallet built on a smartcard device in small format and with low weight. You connect it to a USB port directly in order to manage your account, protect Bitcoins and make safe payments. The Ledger Nano comes built with a number of advanced features.
It can be used on any PC, Mac or Linux machine and is compatible with the Chrome application on Windows 7+, Mac 10.8+, Linux and Chrome OS. It is small sized and light, and updates are free. The Ledger Nano S uses standard USB ports and can also be operated on a mobile with a USB adapter. The management interface is an application for Google Chrome, user-friendly and accessible. The way the Nano S works is that the Bitcoins are kept secure by using a microchip and a PIN. Transactions are verified by using a second factor to satisfy anti-malware priorities.
The Ledger Nano S is completely malware proof – You can authenticate payments even on compromised machines by using your two-factor security card or push notifications on the smartphone. This is a remarkable and one singularly notable capability of the Ledger Nano S . This allows the Nano S to be operated in environments where you would shudder to use other types of wallets. The design of the Nano S is such that all sensitive Bitcoin actions are performed inside the secure element integrated on the microchip.
Also, the Bitcoin private keys are never held by the Ledger or third party since they are hard locked inside your smartcard device. This is another noteworthy feature of the Nano S because it virtually gives you an iron-clad assurance that no application or person can access the private keys by any means. Your account can be restored from a backup if you lose your Nano S or if it’s stolen. This makes the usage of the Nano S virtually worry free. Due to the requirement of a PIN, even if a Nano S is lost, there is very little that can be done by a hacker attempting to crack it.


Trezor
Trezor is a secure transaction signing and Bitcoin storage tool which is one of the leading solutions in the market notable for its security related features. One of the best Bitcoin wallets supports Windows 7+, OS X 10.8+ and Linux. The security related features are rock solid with each Trezor having a PIN code. This means that even if the computer with which the Trezor is being used has been hacked into, the PIN can never be known by any person or application. Bear in mind that the generation of private keys happens on the device and the keys never leave the device. This again provides a complete assurance that no one can access the private keys from a Trezor other than authorized parties.
The Trezor generates a recovery seed at the exact moment when device initialization happens. This seed can be used to recover all contents including private keys and transaction history if your Trezor gets stolen or lost. This is again a one of a kind feature found with the Trezor. This means that even a theft or loss of a Trezor will not do catastrophic damage to you.
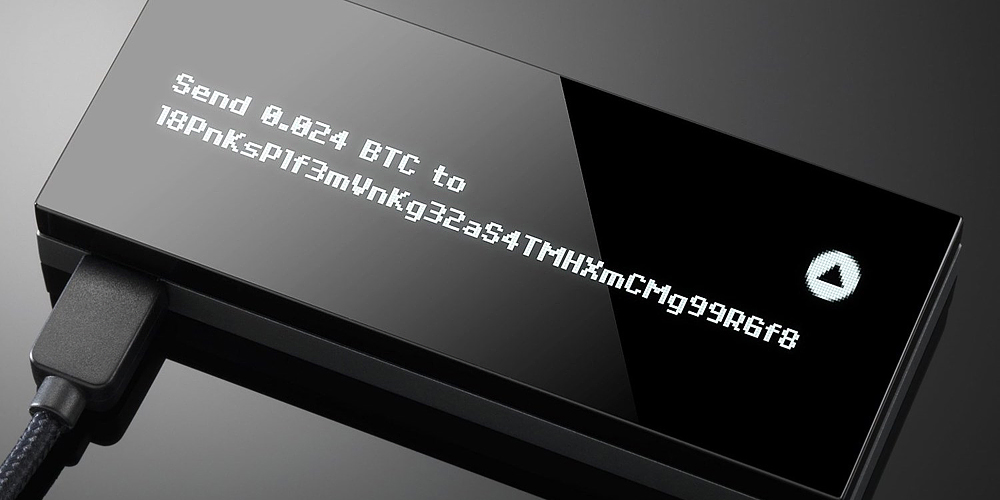
The way a Trezor implements transaction signing is quite unique. When a user wants to make a transaction, the software merely sends a transaction template to the Trezor device and requests a digital signature. With the Trezor device then displaying the exact amount that has been requested and the target address, you can go ahead and confirm the action by pressing the right hardware button. The Trezor device would sign the action internally and send only the digital signature back to the computer while holding onto the private keys internally. All this makes Trezor one of the most secure Bitcoin wallets available at the market.



Trezor model T
TREZOR T emerges as a feature packed and long lasting hardware wallet for cryptocurrency enthusiasts, filling a massive void in the cryptocurrency wallets market. TREZOR T’s touch screen makes it unique; plug the device in and tap in your instructions via the touch screen. TREZOR T builds a lot on the predecessor TREZOR One, and makes a strong case as a powerful, feature rich, user friendly, and highly secure hardware wallet for cryptocurrencies. It offers you pretty much all the TREZOR One features, and a lot more on top of it.
The TREZOR T brings an advanced suite of security features to you. The touch-screen becomes your data entry interface, which means that no one will see your PIN on the Recovery seed, as long as you protect it while entering. Also, the on-screen PIN entry means the TREZOR T doesn’t have to communicate with your computer before you unlock it. Also, the keypad numbers change their order, to ensure that smudges from your fingerprints on the screen don’t reveal your PIN. You can even see your cryptocurrency balances directly on the touch screen of the TREZOR T.
TREZOR T operates on a new firmware called TREZOR Core, which brings together the best of all worlds from TREZOR’s past products and experiences. TREZOR Core is open source and available for adaptation. The code has been written with scalability and expansion in mind; you can hence add new functions, and expand the capabilities of TREZOR T to supporting more cryptocurrencies. Functionalities that were too difficult to code earlier can work easily with TREZOR T’s Core open source code. The ARM Cortex-M4 processor clocked @ 168 Mhz makes TREZOR T one of the most power packed cryptocurrency wallets going around. TREZOR T has you covered in every aspect of connectivity. It is ready for all kinds of integrations, runs a super fast processor, and has a micro SD slot with USB C connector for quick connectivity even when you’re on the move. Device backup and restoration functionalities also ensure you can trust TREZOR T. The dimensions of this hardware wallet are 64mm x 39mm x 10mm – that’s pretty sleek. Sleek, simple, and secure – that’s the crispiest way to describe TREZOR T. Its touch screen, by far, makes it the most advanced hardware cryptocurrency wallet.



KeepKey
The KeepKey is a device for storing and securing your Bitcoins that is based on a USB interface. The way the KeepKey is designed is that when you are configuring and using it, you would need to review and approve every single Bitcoin transaction to be made through the confirmation and display facility it offers. One convenient feature of the KeepKey is that it works with your existing wallet software by taking up the management of private key generation, transaction signing and private key storage.
Its recovery feature works in such a fashion that a rotating cipher is used to restore with a recovery seed. This means that private keys need not be stored on Keepkey. Keepkey creates a private key by using its random number generator, combining it with the randomness from your computer. This lends extra strength to the randomness characteristics due to the usage of two sources of randomness.


Ledger HW.1
[ buy on Amazon ]
The Ledger HW.1 is a wallet built on a tiny smartcard device which can be used as a Bitcoin hardware wallet. Although it shares some characteristics with the Ledger Nano S, it is a slightly different type of device. The wallet is available in 3 editions – Classic, Enterprise and Multisig. Free software updates are available for all the versions. There are a couple of notable features of this wallet. It can be used for wallets being shared by several people. Also, multi-signature based design increases the difficulty of Bitcoins being stolen given that a number of keys are required for each payment.
The Ledger HW.1 device is supported on Mac, PC and Linux and it connects directly to a USB port. This wallet permits you to safely store the Bitcoins offline and make regular online payments. In case of loss, it can be restored on any compatible solutions including other ledger wallets. It uses two factor authentications to verify transactions. A microchip which is locked with a PIN code secures your Bitcoins.
HW.1 is an abbreviated wording for hardware wallet. With a number of enterprise features and a minimalist design, the Ledger HW.1 is a low-budget secure wallet. It is a professional style wallet well customized to your needs. It is available in different packs – pack of 1 HW.1 is the Classic offering, a 3 pack is the HW.1 Multisig and a 10 pack is the HW1 Enterprise. Inside each pack, you have a security key, a HW.1 chip and a recovery sheet. MultiSig significantly increases the difficulty level associated with stealing your Bitcoins owing to the fact that multiple keys are needed for every payment. It can also be employed in situations where wallets are being shared by many people, where a quota is needed in order to spend the coins. One of the most significant advantages of Ledger HW.1 comparing to other hardware wallets is a low price – around $20. Also it’s the smallest one among hardware wallets.



Hardware wallets represent a unique and compelling approach to the environmental needs that demand wallets. With security built in, most of these wallets provide a hardware solution to the needs of handling Bitcoin in particular, and various types of digital currency in general.
What are Bitcoin hardware wallets?
These are dedicated hardware built specifically to store cryptocurrency securely. A hardware wallet can work online to help you make transactions, and can then be taken offline to safely keep the cryptocurrency data. These hardware devices are pretty compact in size, small enough to fit the average person’s pant pockets, much like a wallet.
A hardware wallet generally looks similar to a compact portable hard drive. These wallets are made to withstand all kind of stresses, and are as close to being indestructible as possible. All your cryptocurrency wallet information is stored within this small yet sturdy hard drive, called the hardware wallet. Most critical information is about your private keys, which are equivalent of your Bitcoins.
Now, it’s inherently unsafe to keep the private keys’ information on your desktop or smartphone, because of the ease with which seasoned hackers can access data residing there. Hardware wallets acknowledge and remedy this problem by delivering a mechanism of complete isolation between the private keys and the easy to hack smartphone or computer.
Hardware wallets come in many forms today, with configurations ranging right from mini hard disks to USB drives, from credit sticks to smart-cards. Hardware wallets have been witnessing increasing popularity because Bitcoin and other cryptocurrency owners want to keep their valuable digital keys secure and safe. Companies are competing to develop and launch hardware wallets that come with additional features and functionalities apart from the safekeeping of private keys. In the next sections, we’ll tell you more about the working, applications, and benefits of hardware wallets.
How do hardware wallets work?
Hardware wallets comprise of 2 components – a connected device, and a disconnected part. This design helps hardware wallets deliver maximum security to ensure safekeeping of Bitcoins. Now, hardware thefts can be physically stolen. However, compared to paper wallets, they’re more secure because there’s no step of using software to load private keys in wallet import format. Because such software can often be vulnerable to cyber attacks, hardware wallets become inherently safer than paper wallets.
In a hardware wallet, the connected component holds the public keys, and hence, it can perform all features of a standard wallet. It can choose which transactions to sign, but can’t go ahead and commit the sign, because the private key required for the same is held in the offline device. So, you need to connect the hardware wallet to a computer. This is mostly done via a USB connection, although advanced hardware wallets allow for QR code based connections as well. Once connected, for instance, via USB, the chosen transaction is sent to the offline device (which is now connected). Next, the transaction is signed, and sent back to the wallet. Subsequently, it is sent to the Bitcoin network for verification and to be included in the blockchain.
In hardware wallets that use QR codes based connectivity, things work slightly differently. First up, the transaction is assembled and converted to a QR code. The code is scanned by the offline device, the resulting transaction is signed, again converted to a QR code which is scanned back to the online program. This program then sends the signed QR code to the Bitcoin network for verifications. A QR code based hardware wallet is even more secure than a USB based wallet.
Apart from USB and QR code based hardware wallets, there are other versions that use pin codes. The basic working mechanism, however, remains same – that is, the isolation of the all important private keys from the vulnerabilities of smartphones, PCs, and online software.
Why hardware wallets are the most secure for cryptocurrencies storage?
To answer this question, let’s take a look at the other wallet options that users have.
- Desktop wallets: These come in the form of desktop apps that connect to the cryptocurrency client directly. Now, if your computer is hacked, the hackers will be able to access the app. Malware, key loggers, identify theft – there are so many ways in which desktop wallets can be compromised.
- Paper wallets: More than anything, paper wallet is the practice of printing the public and private keys on a paper, or printing equivalent QR codes on paper, and then keeping it safe for use when needed. Paper wallets, hence, are vulnerable to being lost, damaged, torn, burnt, and faded.
- Mobile wallets: Much like desktop wallets, these are in the form of mobile friendly applications that connect to the crypto currency’s client. The vulnerabilities of desktop wallets hold true for mobile wallets as well.
- Online wallets: These are web based wallets which are accessed via a web link, and hosted on a server managed by the wallet service provider. Though these wallets use encryption, there have already been instances where they’ve been hacked.
The common problem in all these wallet options, apart from paper wallets, is that the public and private keys are stored in one or the other digital form on devices or servers that can be hacked. Paper wallets suffer from their own limitations. This makes hardware wallets among the most secure options of cryptocurrency keys storage for users.
Advantages of Bitcoin hardware wallets
Apart from the cutting edge security, safety from cyber attacks and unauthorized access, and the consequent peace of mind, hardware wallets offer other benefits. Let’s have a look.
- Easy to Set up And Use: With time, hardware wallets have become super easy to set up for users. Most of them just need to be connected to a computer, after which users can see on-screen instructions, and quickly set up the wallet. Also, using it to make transactions is super easy, quick, and secure.
- Secondary Recovery Mechanisms: There’s always the chance that you could misplace or lose your hardware wallet. To make sure you don’t lose your money, modern hardware wallets let you set up recovery phrases, recovery passwords, and other similar recovery mechanism that can help you access your Bitcoins even if you lose the wallet.
- Multi factor Authentication: Hardware wallets use multi-factor authentication to help you live with the peace of mind that even if it’s stolen, nobody will be able to log in, because they would not have access to the secondary device, such as your smartphone, which will be necessary for log in.
- Compatibility with OS and Major Crypto Currencies: Except your hardware wallet to be compatible with the 4 major operating systems – Windows, Linux, MacOS, and Android. Plus, you can store other cryptocurrencies in your hardware wallet apart from Bitcoins.
- Open source software: Most hardware wallets use open source software, which means users can validate pretty much everything about the software and the device’s operations.
Disadvantages of hardware wallets
We’ll round this guide up with a quick take on some disadvantages of hardware wallets.
- Swapping of Recipient Address: Hardware wallets are not quite able to save you from malware led manipulations where in the recipient’s address can be swapped, causing the Bitcoins to be sent to unintended parties.
- Insecure Random Number Generator: Most Bitcoin hardware wallets use RNGs in their mechanism. Now, if the RNG itself is weak, and predictable, it can lead to several fail cases, putting money at risk in high value transactions.
- Compromised Firmware, Software, and Hardware: To some extent, you can verify and validate the working of the software, because it’s mostly open source. However, there can always be hardware and firmware flaws that can put the hardware wallet at risk.
- Unpredictable Shipping Process: When you buy a hardware wallet and the seller ships it to you, there are several intermediary steps wherein unscrupulous agents can replace the genuine device with a counterfeit one, or insert backdoors into the original devices. That’s why we strongly recommend to buy Bitcoin hardware wallets on official sites or Amazon, where you will get original device but not a forgery. Never buy hardware wallets from someone or on Ebay – you’ll never be sure that your hardware wallet works as it must work.
You’d agree that most of the disadvantages cited above are not exclusively tied to hardware wallets, and can affect pretty much any kind of wallet. The bottom line is that hardware wallets have proven their effectiveness in keeping cyber currencies safe and secure for users.





